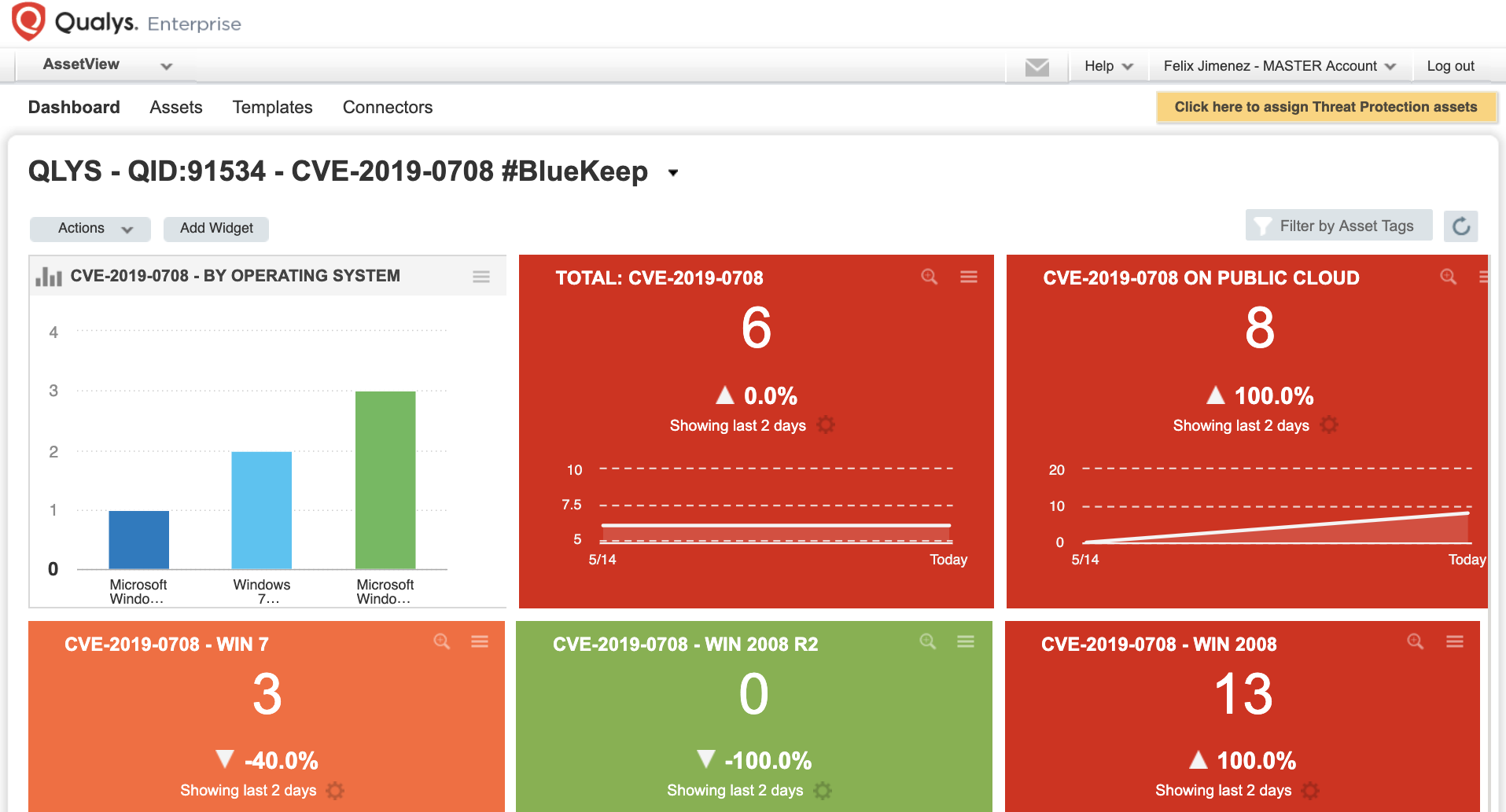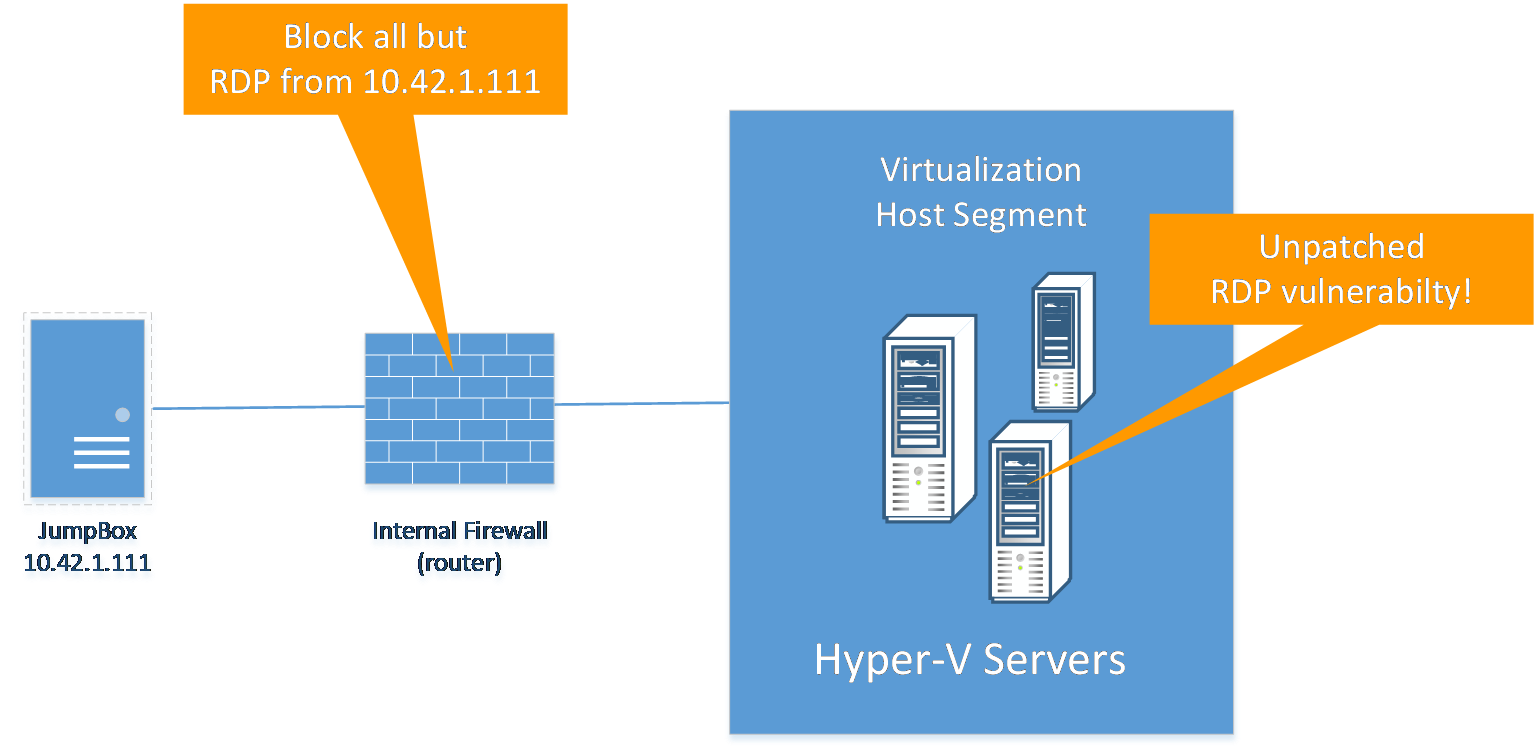
Correlating Vulnerability Scans with Network Path Analysis to Find and Remediate the Biggest Risks to Your Network and Avoid Wasting Time on the Little Ones
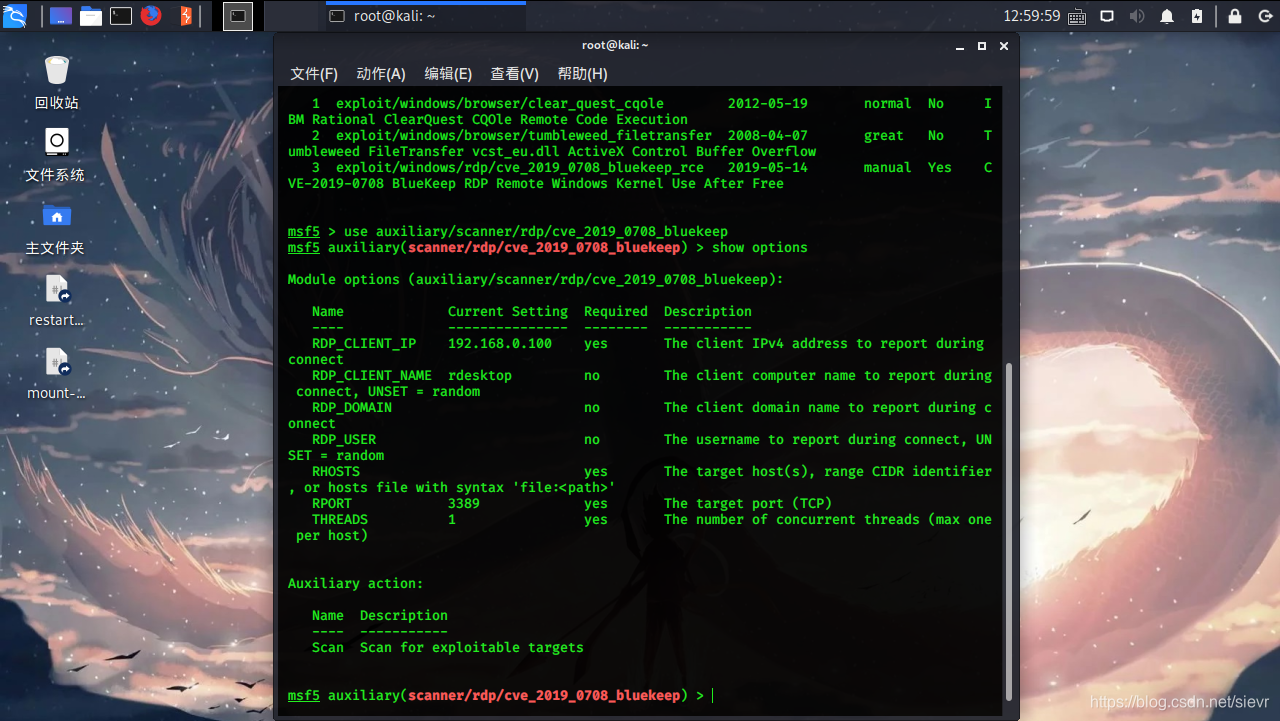
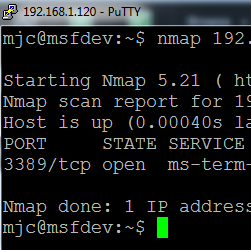
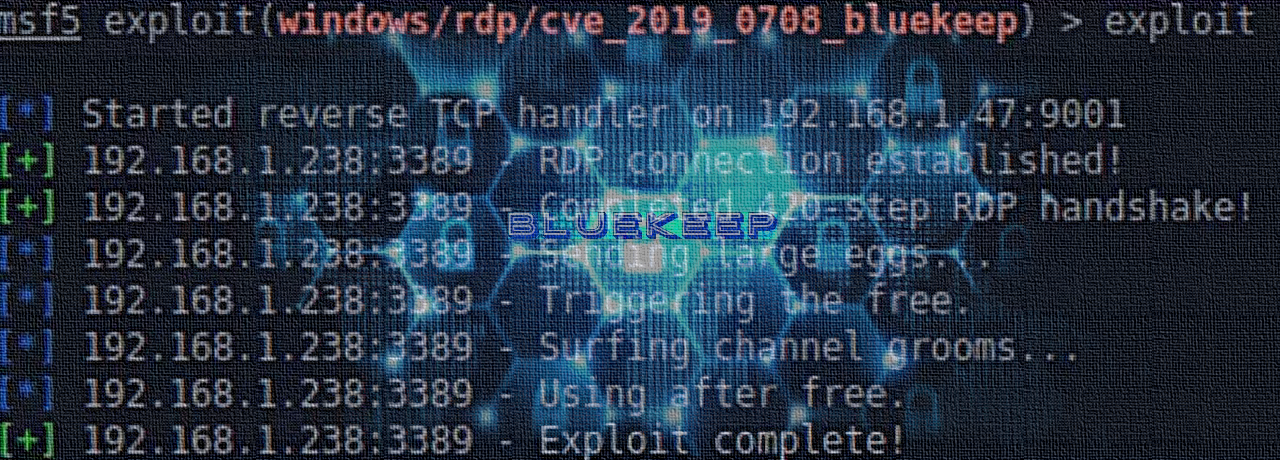
Cisco Talos Intelligence Group - Comprehensive Threat Intelligence: Using Firepower to defend against encrypted RDP attacks like BlueKeep
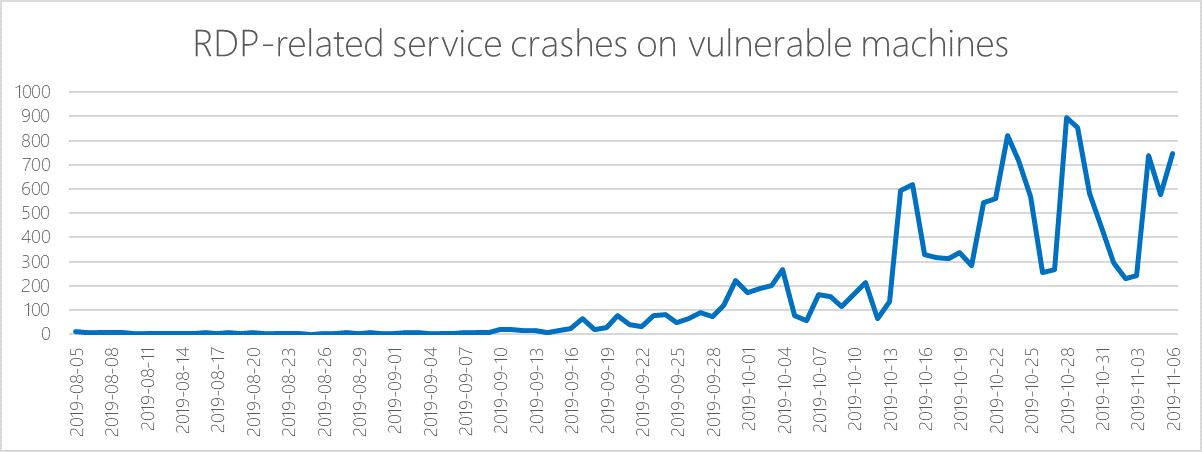
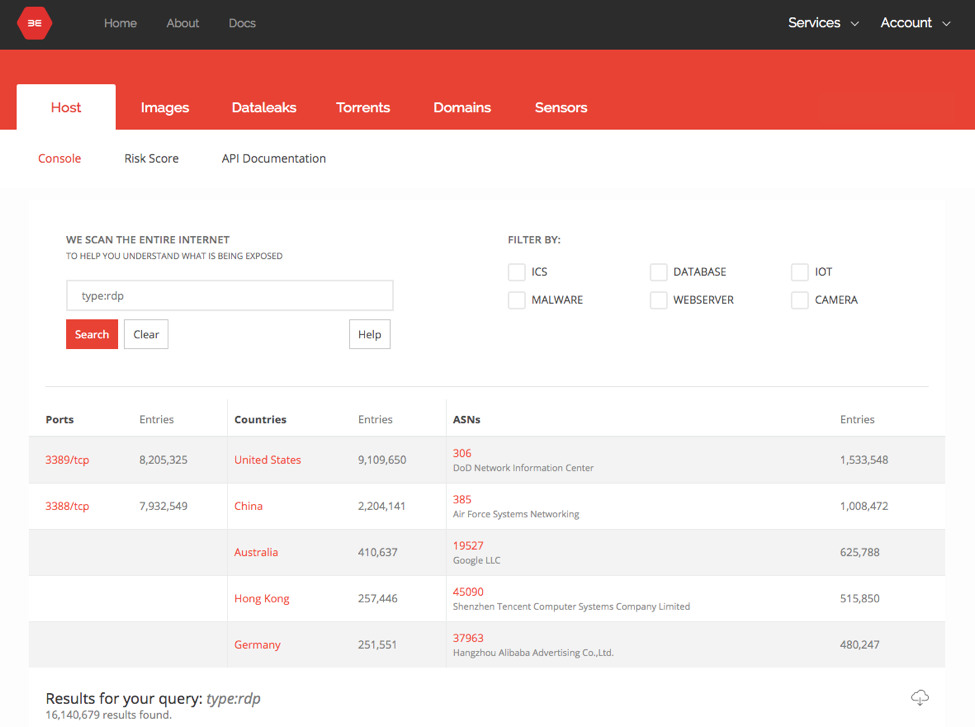
Microsoft works with researchers to detect and protect against new RDP exploits - Microsoft Security Blog